Catatan Lain
Malware dan PHP Shell Scanner Untuk Server UNISM.ac.id
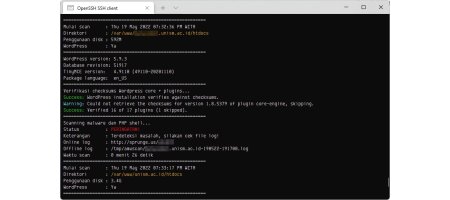
Wrapper script WP-CLI dan PHP Malware Scanner yang saya buat untuk melakukan scanning seluruh domain unism.ac.id yang berada di cloud server. Jika terdeteksi adanya celah/malware, maka file log akan disimpan sebagai log lokal dan juga diunggah ke internet (sprunge.us). Bisa di integrasikan dengan bot Telegram untuk laporan jika terdeteksi malware. Script juga dapat dijalankan secara otomatis dengan menggunakan cron scheduler.
#!/bin/bash
# wrapper wp-cli dan php-antimalware
# coded by Fajar Ramadhan
# tested on Ubuntu 20.04 & Debian 10
logdir=/tmp/amwscan
if [ -d "$logdir" ]; then
mkdir /tmp/awmscan >/dev/null 2>&1
fi
if ! command -v wp >/dev/null 2>&1
then
echo "WP-CLI tidak ditemukan. Menginstal WP-CLI..."
curl -sS https://raw.githubusercontent.com/wp-cli/builds/gh-pages/phar/wp-cli.phar > /usr/local/bin/wp
chmod +x /usr/local/bin/wp
export PATH=$PATH":/usr/local/bin"
fi
if ! command -v awscan >/dev/null 2>&1
then
echo "PHP Anti-Malware Scanner tidak ditemukan. Menginstal AMWScan..."
curl -sS https://raw.githubusercontent.com/marcocesarato/PHP-Antimalware-Scanner/master/dist/scanner > /usr/local/bin/awscan
printf "#!/bin/bash\nphp /usr/local/bin/awscan.phar \$@" > /usr/local/bin/awscan
chmod u+x,g+x /usr/local/bin/awscan.phar
chmod u+x,g+x /usr/local/bin/awscan
export PATH=$PATH":/usr/local/bin"
fi
date=$(date '+%d%m%y-%H%M%S')
check_wp="wp-includes/version.php"
scanner=/usr/local/bin/awscan
printf "%60s\n" | tr ' ' '='
echo
echo " Wrapper Script WP-CLI + PHP-Antimalware v1.0"
echo " Coded by Fajar Ramadhan (inbox@fazar.net)"
echo
printf "%60s\n" | tr ' ' '='
# path webroot /var/www/domain.xxx/htdocs
find /var/www -maxdepth 2 -mindepth 1 -name "htdocs" -type d | while read dir ; do
start=`date +%s`
cd $dir
printf "%-15s : %-10s\n" "Mulai scan" "$(date)" "Direktori" "$(tput setaf 3)"$dir"$(tput sgr0)" "Penggunaan disk" "$(du -sh $dir | awk '{ print $1 }')"
if [ -f "$check_wp" ]; then
printf "%-15s : %-10s\n" "WordPress" "Ya"
printf "%54s\n" | tr ' ' '='
wp core version --extra --allow-root
printf "%54s\n" | tr ' ' '='
echo "Verifikasi checksums Wordpress core + plugins..."
wp core verify-checksums --allow-root
wp plugin verify-checksums --all --allow-root
else
printf "%-15s : %-10s\n" "WordPress" "Tidak"
fi
printf "%54s\n" | tr ' ' '='
domain=$(pwd | awk -F'/' '$0=$(NF-1)')
echo "Scanning malware & PHP shell => $domain"
php $scanner . -l -r --report-format txt --path-report $logdir/$domain-$date.log --silent > /dev/null 2>&1
logline=$(< "$logdir/$domain-$date.log" wc -l)
if [ $logline -lt 2 ]
then
printf "%-15s : %-10s\n" "Status" "$(tput setaf 2)"OK"$(tput sgr0)" "Keterangan" "Tidak terdeteksi masalah"
else
sendUrl=$(curl -sS -F 'sprunge=<-' http://sprunge.us < $logdir/$domain-$date.log)
printf "%-15s : %-10s\n" "Status" "$(tput setaf 1)"PERINGATAN!"$(tput sgr0)" "Keterangan" "Terdeteksi masalah, silakan cek file log!" "Online log" "$sendUrl" "Offline log" "$logdir/$domain-$date.log"
fi
end=`date +%s`
runtime=$( echo "$end - $start" | bc -l );
minutes=$(( (runtime % 3600) / 60 ));
seconds=$(( (runtime % 3600) % 60 ));
printf "%-15s : %-10s\n" "Waktu scan" "$minutes menit $seconds detik"
printf "%54s\n" | tr ' ' '='
sleep 10
done
# endContoh output script saat dieksekusi:
Load Balancer
# software id = 3UNI-XXXX
#
# model = RB1100x4
# serial number = XXXXXXXXXXXXXXXX
/interface ethernet
set [ find default-name=ether1 ] comment="Telkom #1"
set [ find default-name=ether2 ] comment="Telkom #2"
set [ find default-name=ether3 ] comment=Distribusi
/interface list
add name=WAN
add name=LAN
/routing table
add fib name=to_ISP1
add fib name=to_ISP2
/ip settings
set allow-fast-path=no
/interface list member
add interface=ether1 list=WAN
add interface=ether2 list=WAN
add interface=ether3 list=LAN
/ip address
add address=192.168.50.1/24 interface=ether3 network=192.168.50.0
add address=10.0.10.25/24 interface=ether1 network=10.0.10.0
add address=10.0.30.25/24 interface=ether2 network=10.0.30.0
/ip dns
set allow-remote-requests=yes servers=8.8.8.8,8.8.4.4
/ip dns static
add address=192.168.50.1 name=lb.campus.unism.local
/ip firewall address-list
add address=192.168.50.0/24 list=local
/ip firewall mangle
add action=accept chain=prerouting comment="traceroute & ping" \
dst-address-list=!local in-interface-list=LAN protocol=icmp
add action=accept chain=prerouting comment="allow local to internet" \
dst-address-list=local in-interface-list=LAN
add action=mark-connection chain=prerouting connection-mark=no-mark \
connection-state=established,related in-interface=ether1 \
new-connection-mark=ISP1_conn passthrough=yes
add action=mark-connection chain=prerouting connection-mark=no-mark \
connection-state=established,related in-interface=ether2 \
new-connection-mark=ISP2_conn passthrough=yes
add action=mark-connection chain=prerouting connection-mark=no-mark \
dst-address-list=!local dst-address-type=!local in-interface-list=LAN \
new-connection-mark=ISP1_conn passthrough=yes per-connection-classifier=\
both-addresses-and-ports:2/0
add action=mark-connection chain=prerouting connection-mark=no-mark \
dst-address-list=!local dst-address-type=!local in-interface-list=LAN \
new-connection-mark=ISP2_conn passthrough=yes per-connection-classifier=\
both-addresses-and-ports:2/1
add action=mark-routing chain=prerouting connection-mark=ISP1_conn \
in-interface-list=LAN new-routing-mark=to_ISP1 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=ISP2_conn \
in-interface-list=LAN new-routing-mark=to_ISP2 passthrough=yes
add action=mark-routing chain=output connection-mark=ISP1_conn \
dst-address-list=!local new-routing-mark=to_ISP1 passthrough=yes
add action=mark-routing chain=output connection-mark=ISP2_conn \
dst-address-list=!local new-routing-mark=to_ISP2 passthrough=yes
/ip firewall nat
add action=masquerade chain=srcnat ipsec-policy=out,none out-interface-list=\
WAN
/ip route
add comment=ISP1 disabled=no distance=1 dst-address=9.9.9.9/32 gateway=\
10.0.10.1 pref-src=0.0.0.0 routing-table=main scope=10 \
suppress-hw-offload=no target-scope=10
add comment=ISP2 disabled=no distance=1 dst-address=8.26.56.26/32 gateway=\
10.0.30.1 pref-src=0.0.0.0 routing-table=main scope=10 \
suppress-hw-offload=no target-scope=10
add check-gateway=ping distance=1 dst-address=0.0.0.0/0 gateway=9.9.9.9 \
scope=10 target-scope=11
add check-gateway=ping distance=1 dst-address=0.0.0.0/0 gateway=8.26.56.26 \
scope=10 target-scope=11
add comment=ISP1 disabled=no distance=1 dst-address=64.6.64.6/32 gateway=\
10.0.10.1 pref-src=0.0.0.0 routing-table=main scope=10 \
suppress-hw-offload=no target-scope=10
add comment=ISP1 disabled=no distance=1 dst-address=208.67.220.220/32 \
gateway=10.0.10.1 pref-src=0.0.0.0 routing-table=main scope=10 \
suppress-hw-offload=no target-scope=10
add comment=ISP2 disabled=no distance=1 dst-address=208.67.222.222/32 \
gateway=10.0.30.1 pref-src=0.0.0.0 routing-table=main scope=10 \
suppress-hw-offload=no target-scope=10
add comment=ISP2 disabled=no distance=1 dst-address=64.6.65.6/32 gateway=\
10.0.30.1 pref-src=0.0.0.0 routing-table=main scope=10 \
suppress-hw-offload=no target-scope=10
add check-gateway=ping distance=1 dst-address=0.0.0.0/0 gateway=64.6.64.6 \
routing-table=to_ISP1 scope=10 target-scope=11
add check-gateway=ping distance=2 dst-address=0.0.0.0/0 gateway=64.6.65.6 \
routing-table=to_ISP1 scope=10 target-scope=11
add check-gateway=ping distance=1 dst-address=0.0.0.0/0 gateway=\
208.67.222.222 routing-table=to_ISP2 scope=10 target-scope=11
add check-gateway=ping distance=2 dst-address=0.0.0.0/0 gateway=\
208.67.220.220 routing-table=to_ISP2 scope=10 target-scope=11
/system clock
set time-zone-name=Asia/Makassar